Introduction
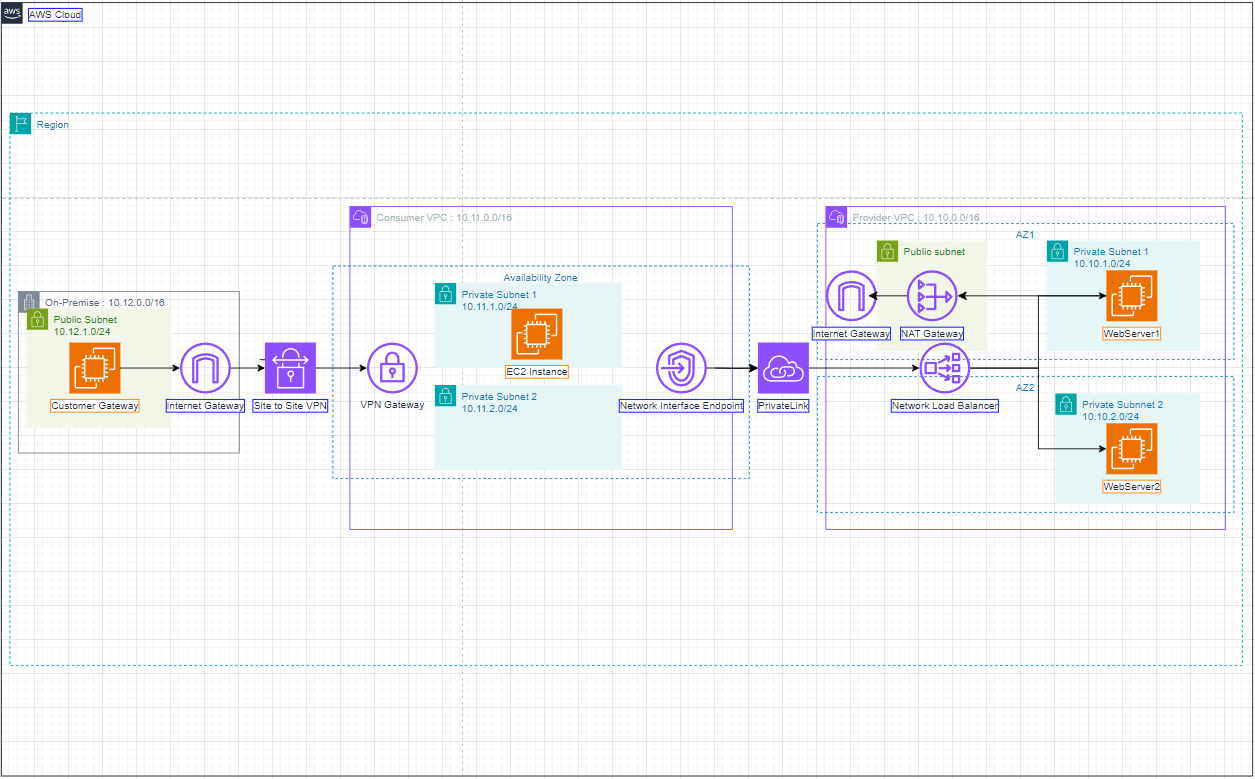
Introducing AWS PrivateLink
AWS PrivateLink is a highly available, scalable technology that you can use to privately connect your VPC to services as if they were in your VPC. You do not need to use an internet gateway, NAT device, public IP address, AWS Direct Connect connection, or AWS Site-to-Site VPN connection to allow communication with the service from your private subnets. Therefore, you control the specific API endpoints, sites, and services that are reachable from your VPC.
Service providers
The owner of a service is the service provider. Service providers include AWS, AWS Partners, and other AWS accounts. Service providers can host their services using AWS resources, such as EC2 instances, or using on-premises servers.
Endpoint services
A service provider creates an endpoint service to make their service available in a Region. A service provider must specify a load balancer when creating an endpoint service. The load balancer receives requests from service consumers and routes them to your service. By default, your endpoint service is not available to service consumers. You must add permissions that allow specific AWS principals to connect to your endpoint service.
Service names
Each endpoint service is identified by a service name. A service consumer must specify the name of the service when creating a VPC endpoint. Service consumers can query the service names for AWS services. Service providers must share the names of their services with service consumers.
Service states
The following are the possible states for an endpoint service:
- Pending - The endpoint service is being created.
- Available - The endpoint service is available.
- Failed - The endpoint service could not be created.
- Deleting - The service provider deleted the endpoint service and deletion is in progress.
- Deleted - The endpoint service is deleted.
Service consumers
The user of a service is a service consumer. Service consumers can access endpoint services from AWS resources, such as EC2 instances, or from on-premises servers.
VPC endpoints
A service consumer creates a VPC endpoint to connect their VPC to an endpoint service. A service consumer must specify the service name of the endpoint service when creating a VPC endpoint. There are multiple types of VPC endpoints. You must create the type of VPC endpoint that’s required by the endpoint service.
- Interface - Create an interface endpoint to send TCP traffic to an endpoint service. Traffic destined for the endpoint service is resolved using DNS.
- GatewayLoadBalancer - Create a Gateway Load Balancer endpoint to send traffic to a fleet of virtual appliances using private IP addresses. You route traffic from your VPC to the Gateway Load Balancer endpoint using route tables. The Gateway Load Balancer distributes traffic to the virtual appliances and can scale with demand.
There is another type of VPC endpoint, Gateway, which creates a gateway endpoint to send traffic to Amazon S3 or DynamoDB. Gateway endpoints do not use AWS PrivateLink, unlike the other types of VPC endpoints.
Endpoint network interfaces
An endpoint network interface is a requester-managed network interface that serves as an entry point for traffic destined to an endpoint service. For each subnet that you specify when you create a VPC endpoint, we create an endpoint network interface in the subnet.
If a VPC endpoint supports IPv4, its endpoint network interfaces have IPv4 addresses. If a VPC endpoint supports IPv6, its endpoint network interfaces have IPv6 addresses. The IPv6 address for an endpoint network interface is unreachable from the internet. When you describe an endpoint network interface with an IPv6 address, notice that denyAllIgwTraffic is enabled.
The IP addresses of an endpoint network interface will not change during the lifetime of its VPC endpoint.
Endpoint policies
A VPC endpoint policy is an IAM resource policy that you attach to a VPC endpoint. It determines which principals can use the VPC endpoint to access the endpoint service. The default VPC endpoint policy allows all actions by all principals on all resources over the VPC endpoint.
Endpoint states
When you create a VPC endpoint, the endpoint service receives a connection request. The service provider can accept or reject the request. If the service provider accepts the request, the service consumer can use the VPC endpoint after it enters the Available state.
The following are the possible states for a VPC endpoint:
- PendingAcceptance - The connection request is pending. This is the initial state if requests are manually accepted.
- Pending - The service provider accepted the connection request. This is the initial state if requests are automatically accepted. The VPC endpoint returns to this state if the service consumer modifies the VPC endpoint.
- Available - The VPC endpoint is available for use.
- Rejected - The service provider rejected the connection request. The service provider can also reject a connection after it is available for use.
- Expired - The connection request expired.
- Failed - The VPC endpoint could not be made available.
- Deleting - The service consumer deleted the VPC endpoint and deletion is in progress.
- Deleted - The VPC endpoint is deleted.
Introducing VPN Site to Site
One of the most common ways that customers connect securely to AWS from on premises is by using the AWS Site-to-Site VPN managed IPSec VPN solution. One key benefit our customers look for when using the service is not having to manage 3rd-party or custom VPN solutions built using EC2 instances. The native service is already built to be highly-available with two tunnels in two different Availability Zones and has native integration with AWS Transit Gateway (via a VPN attachment) which allows customers to scale the connectivity to multiple VPCs with a single Transit Gateway-based VPN connection.
Concepts
The following are the key concepts for Site-to-Site VPN:
-
VPN connection: A secure connection between your on-premises equipment and your VPCs.
-
VPN tunnel: An encrypted link where data can pass from the customer network to or from AWS.
Each VPN connection includes two VPN tunnels which you can simultaneously use for high availability.
-
Customer gateway: An AWS resource which provides information to AWS about your customer gateway device.
-
Customer gateway device: A physical device or software application on your side of the Site-to-Site VPN connection.
-
Target gateway: A generic term for the VPN endpoint on the Amazon side of the Site-to-Site VPN connection.
-
Virtual private gateway: A virtual private gateway is the VPN endpoint on the Amazon side of your Site-to-Site VPN connection that can be attached to a single VPC.
-
Transit gateway: A transit hub that can be used to interconnect multiple VPCs and on-premises networks, and as a VPN endpoint for the Amazon side of the Site-to-Site VPN connection.