Configure Customer Gateway
Configure Customer Gateway
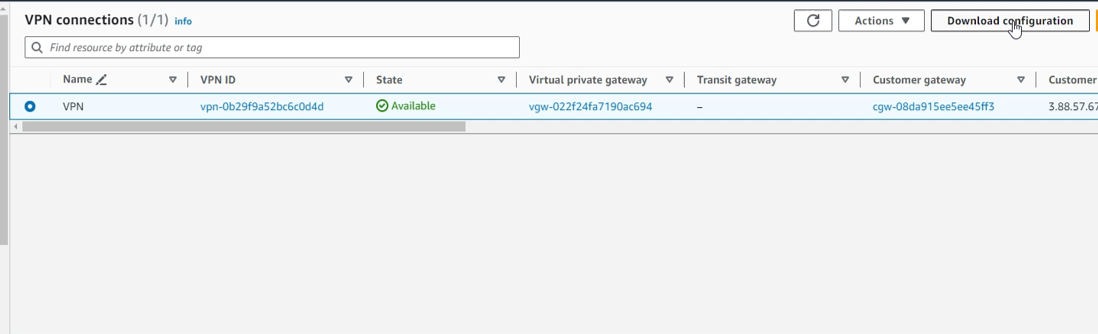
- Access to VPC
- Select Site-to-Site VPN Connection
- Select the created VPN Connection
- Select Download Configuration
- In the Download Configuration dialog box, select the appliance that is appropriate for you: In this exercise, we will use OpenSwan.
- Vendor: Select OpenSwan
- Platform: Select OpenSwan
- Software: Select OpenSwan 2.6.38+
- IKE version: Select ikev1
- Select Download.
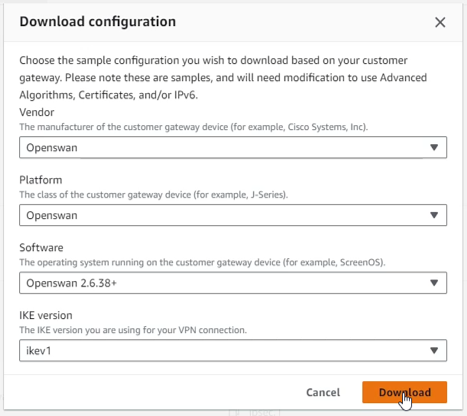
- Save the picture file information to the folder we use to store key pairs and tools for the lab.
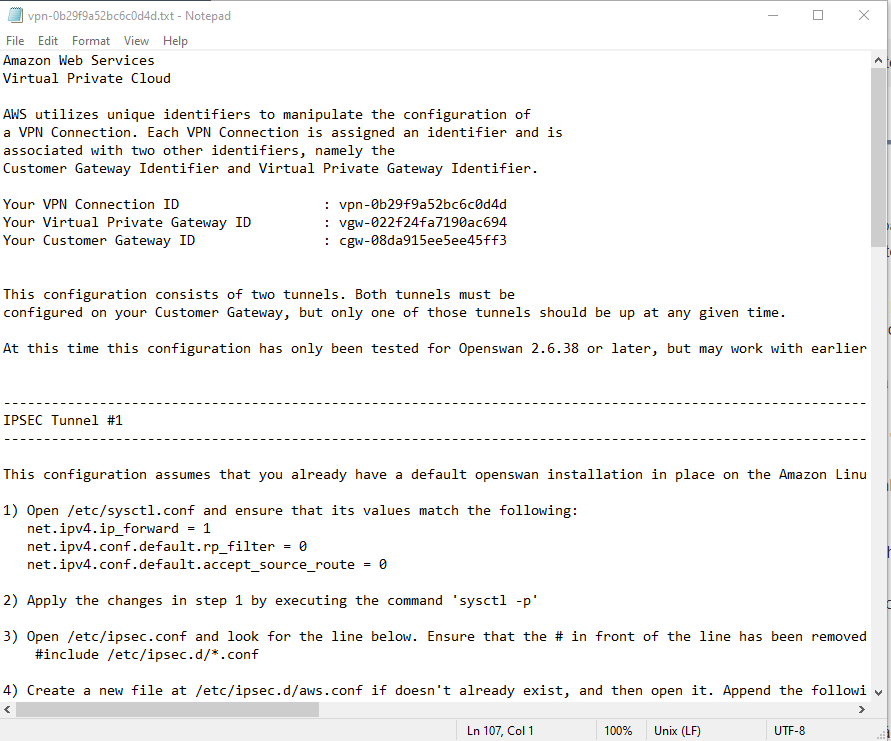
- Then based on the configuration provided, you change the appropriate information and configuration for your device.
- Connect to EC2 Customer Gateway
- In the EC2 interface, select Instances, select Customer GW*, select Connect
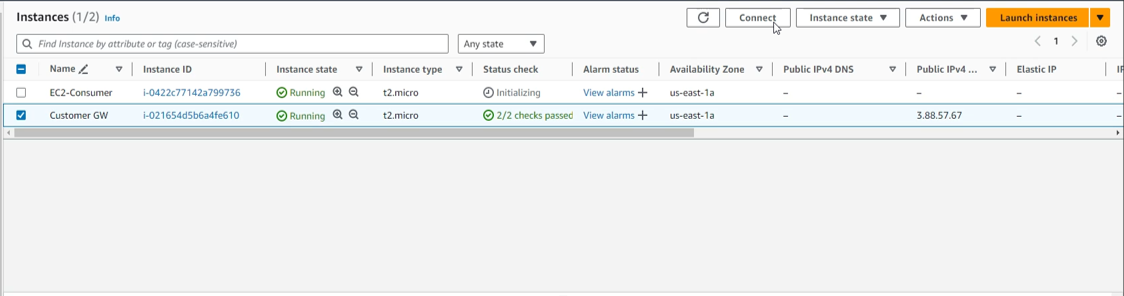
- In the Connect to instance interface
- In the Connection Type section, select Connect using EC2 Instance Connect, because Customer GW belongs to the Public subnet, so we use EC2 Instance Connect
- Select Connect

- Connection completed

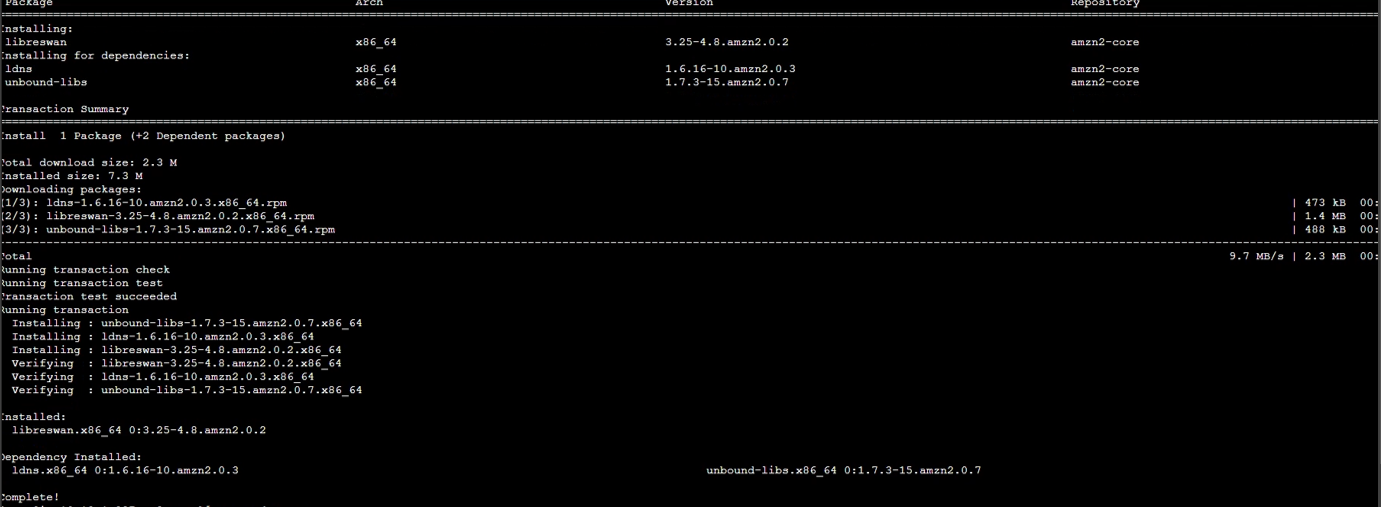
- Install OpenSwan
sudo su
yum install openswan -y
 5. Check the configuration file /etc/ipsec.conf
5. Check the configuration file /etc/ipsec.conf
en /etc/ipsec.conf
- Check the configuration as shown below.
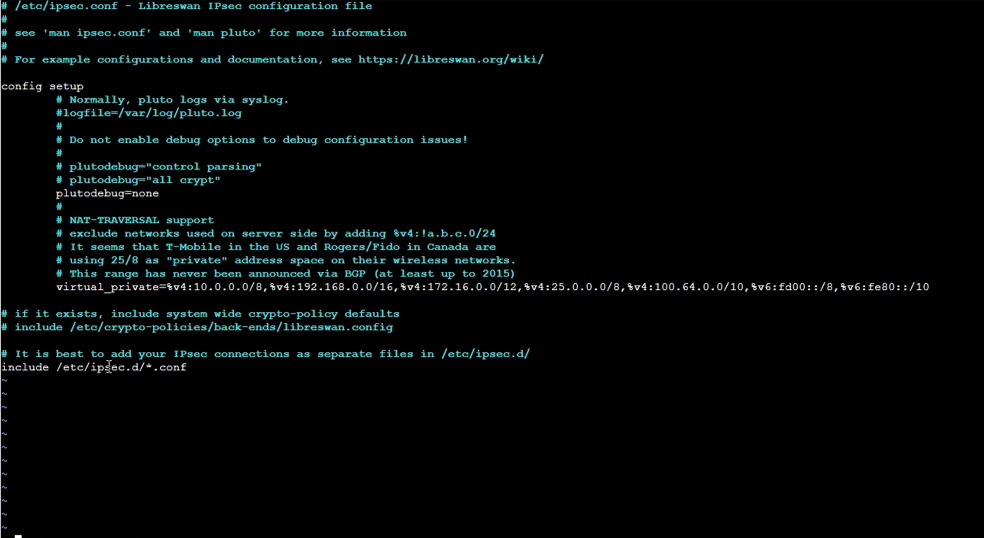
- Press the ESC key and the combination :q! to exit the vi editor.
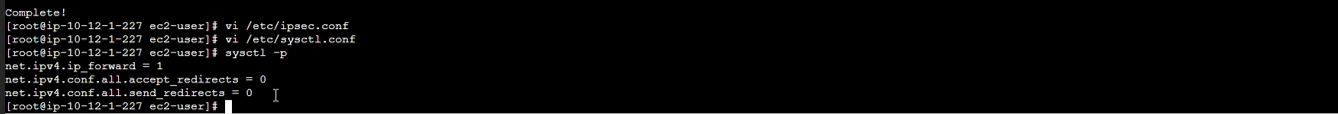
- Configure file /etc/sysctl.conf
en /etc/sysctl.conf
- Press i key to edit the file.
- Add the following snippet to the end of the configuration file
net.ipv4.ip_forward = 1
net.ipv4.conf.all.accept_redirects = 0
net.ipv4.conf.all.send_redirects = 0
- Press the ESC key and the combination :wq! to save the configuration file
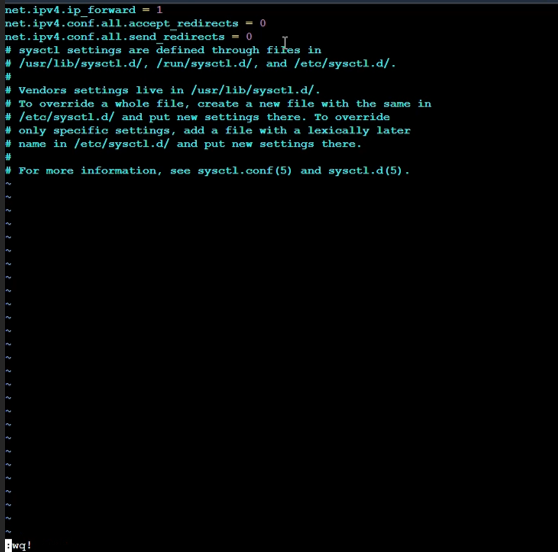
- Then to apply this configuration, run the command:
sysctl -p
 8. Next we will configure the file /etc/ipsec.d/aws.conf
8. Next we will configure the file /etc/ipsec.d/aws.conf
en /etc/ipsec.d/aws.conf
- Press i key to edit the file.
- Add the following snippet to the configuration file. We will create 2 Tunnels with information taken from the VPN Connection configuration file you downloaded and saved in the folder containing the key pair previously.
- Make sure you edit the appropriate IP address and network layer before copying the above configuration.
- For Amazon Linux, we will remove the auth=esp line in the original configuration file.
- Because we only have 1 public IP address for Customer Gateway, we will need to add configuration overlapip=yes.
- leftid: IP Public Address on OnPremise side. (Here is the public IP of EC2 Customer GW in On-Premise VPC).
- right: IP Public Address on AWS VPN Tunnel side.
- leftsubnet: CIDR of Local Network (If there are multiple network layers, you can leave it as 0.0.0.0/0).
- rightsubnet: CIDR of the Private Subnet Network on AWS.
conn Tunnel1
authby=secret
auto=start
left=%defaultroute
leftid=3.88.57.67
right=34.226.49.224
type=tunnel
ikelifetime=8h
keylife=1h
phase2alg=aes128-sha1;modp1024
ike=aes128-sha1;modp1024
keyingtries=%forever
keyexchange=ike
leftsubnet=10.12.0.0/16
rightsubnet=10.11.0.0/16
dpddelay=10
dpdtimeout=30
dpdaction=restart_by_peer
overlapip=yes
conn Tunnel2
authby=secret
auto=start
left=%defaultroute
leftid=3.88.57.67
right=52.70.128.251
type=tunnel
ikelifetime=8h
keylife=1h
phase2alg=aes128-sha1;modp1024
ike=aes128-sha1;modp1024
keyingtries=%forever
keyexchange=ike
leftsubnet=10.12.0.0/16
rightsubnet=10.11.0.0/16
dpddelay=10
dpdtimeout=30
dpdaction=restart_by_peer
overlapip=yes
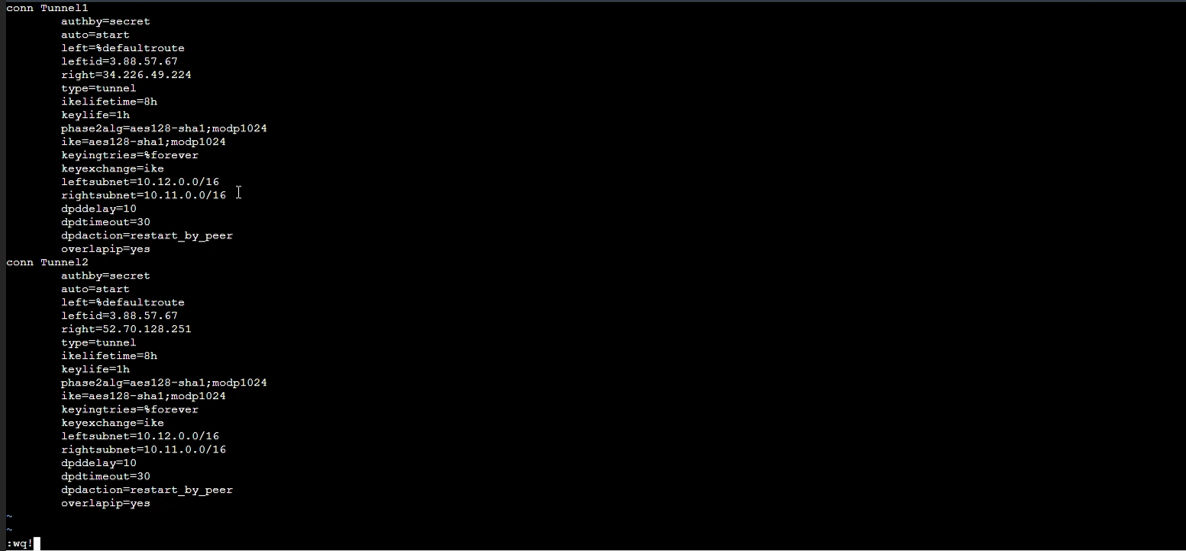
- Press the ESC key and the combination :wq! to save the configuration file
- Check the next step in the configuration file we downloaded.
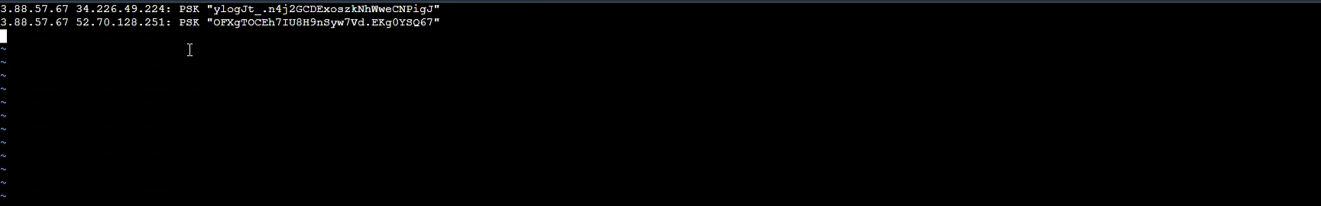
- Create and configure file etc/ipsec.d/aws.secrets Create a new file with the following configuration to set up authentication for 2 Tunnels.
- Run the command vi /etc/ipsec.d/aws.secrets to create files and configurations
touch /etc/ipsec.d/aws.secrets
- Press i key to edit the file.
- Add the following configuration snippet to the end of the configuration file (this config snippet is in step 5 of IPSEC Tunnel #1 and IPSEC Tunnel #2)
- Press the ESC key and the combination :wq! to save the configuration file
- Restart Network service & IPSEC service
systemctl restart network
systemctl enable ipsec.service
systemctl start ipser.service
systemctl status ipser.service
- If the tunnel status is still not running properly, after checking and updating the configuration you will need to run the command to restart the service network and IPsec :
systemctl restart network
systemctl restart ipsec.service
 12. After the service has run, wait a few minutes and then try to ping from the Customer Gateway server to the EC2 Consumer server. If the VPN configuration is successful, you will get the results below.
12. After the service has run, wait a few minutes and then try to ping from the Customer Gateway server to the EC2 Consumer server. If the VPN configuration is successful, you will get the results below.
ping <EC2 Private IP>
